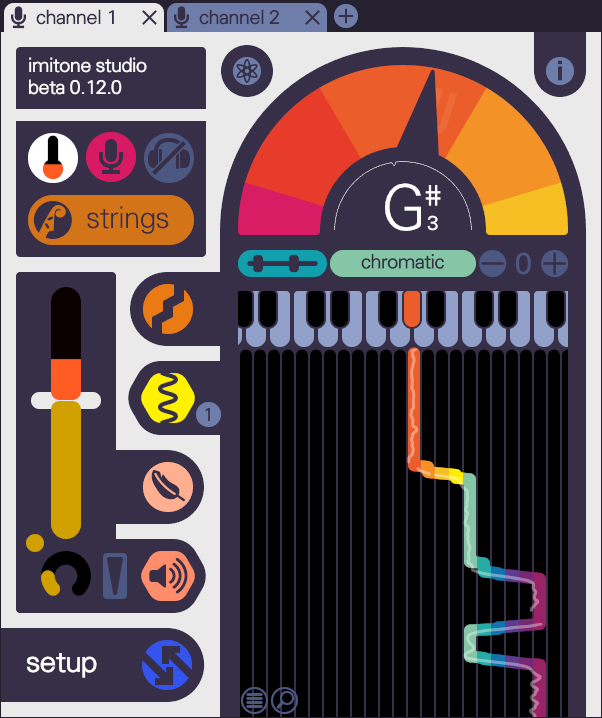
play any instrument with your voice.
explore and create music with only a microphone.

Use the artifacts to determine the specific city where these activities occurred. Recommended Tools Typical tools used for a challenge of this nature include:
Determine the ComputerName of the target device and the MAC address of the Wi-Fi adapter used. Network Artifacts:
For examining Windows Event Logs (if applicable) to find system names and connection timestamps. 3G-L_Gun_Fight.7z
Locate DHCP lease acquisition times and the specific IP addresses assigned at different "café" locations.
Locate a specific "notes" file, identify its name, and extract its contents. Track file downloads performed by the user. Use the artifacts to determine the specific city
Identify the SSIDs of multiple Wi-Fi networks the user connected to.
The file is an artifact from a digital forensics challenge featured in L3akCTF 2025 . It is primarily a network and system forensics exercise that requires participants to analyze data to reconstruct the activities of a specific user. Challenge Overview Locate DHCP lease acquisition times and the specific
The challenge involves answering a series of 14 specific questions based on the contents of the .7z archive. These questions focus on identifying device metadata, network connections, and user behavior across multiple locations (referred to as "cafés" in the challenge text). Key Forensics Objectives
Use the artifacts to determine the specific city where these activities occurred. Recommended Tools Typical tools used for a challenge of this nature include:
Determine the ComputerName of the target device and the MAC address of the Wi-Fi adapter used. Network Artifacts:
For examining Windows Event Logs (if applicable) to find system names and connection timestamps.
Locate DHCP lease acquisition times and the specific IP addresses assigned at different "café" locations.
Locate a specific "notes" file, identify its name, and extract its contents. Track file downloads performed by the user.
Identify the SSIDs of multiple Wi-Fi networks the user connected to.
The file is an artifact from a digital forensics challenge featured in L3akCTF 2025 . It is primarily a network and system forensics exercise that requires participants to analyze data to reconstruct the activities of a specific user. Challenge Overview
The challenge involves answering a series of 14 specific questions based on the contents of the .7z archive. These questions focus on identifying device metadata, network connections, and user behavior across multiple locations (referred to as "cafés" in the challenge text). Key Forensics Objectives