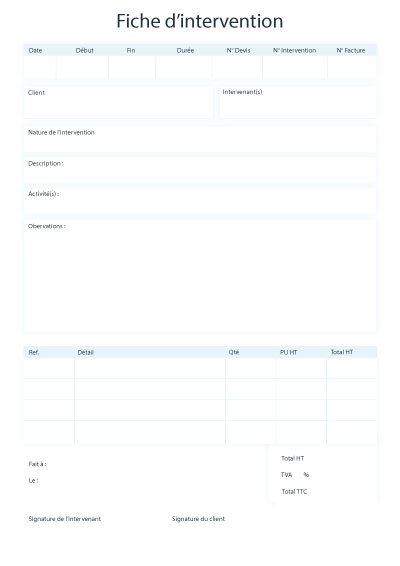
Téléchargez gratuitement
Votre fiche d'intervention
Below is a structured outline you can use to draft a comprehensive report or analysis on this file.
: Link the file's usage to specific DOD Instruction (DODI) guidelines, such as those governing Information Technology (IT) or Cybersecurity (CS). Download File DODIc1t1ssDODI.torrent
: Suggest utilizing dedicated, air-gapped workstations for the initial extraction. Below is a structured outline you can use
: Address how the data within the torrent is handled post-download to prevent data leakage. 5. Risk Assessment : Address how the data within the torrent
: Transitioning from BitTorrent protocols to more modern, decentralized storage solutions like IPFS .
: Detail why a torrent format is selected for this specific file, such as reducing central server load or distributing data across remote nodes with limited bandwidth. 4. Security & Compliance Considerations
: Identify whether the distribution relies on a private tracker (common for DoD or enterprise environments) or Distributed Hash Tables (DHT) like Mainline DHT .