Show Focus Points
2019 update released! Check out download page for details
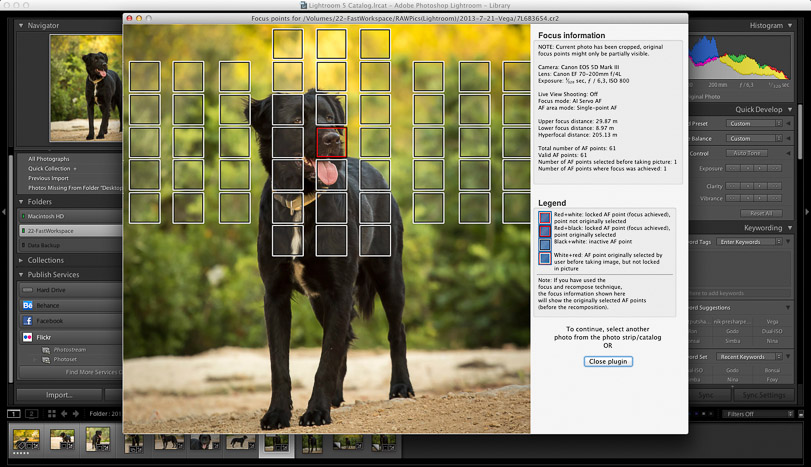
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
Show Focus Points
2019 update released! Check out download page for details
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
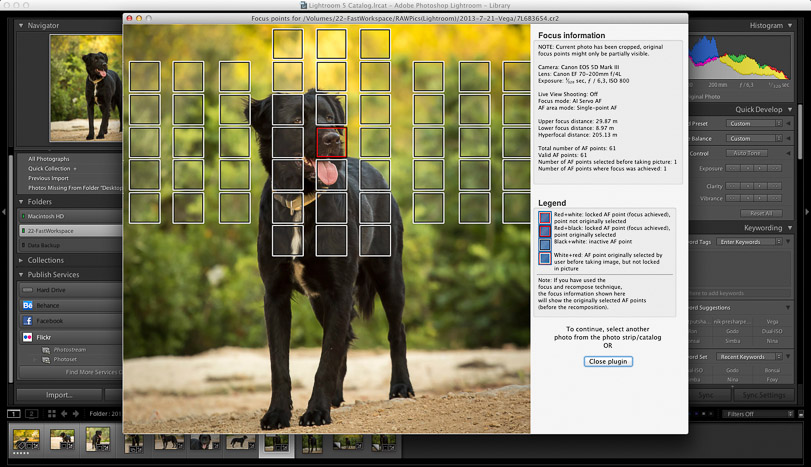
Show Focus Points is a plugin for Adobe Lightroom which shows you which of your camera's focus points were used when you took a picture.
Below find some screenshots of the plugin in action.
Click on the images to enlarge them.
Download Mac-only version (6.6 MB)
Download Windows-only version (14 MB)
Download version containing both Mac+Windows versions (20 MB)
While mathematical proofs on paper provide the theoretical foundation, translating these designs into code introduces the risk of human error and implementation bugs. To bridge this gap, computer scientists utilize formal verification. Formal verification is the act of proving or disproving the correctness of intended algorithms underlying a system with respect to a certain formal specification or property, using mathematical methods. By writing the protocol's specifications and its code in specialized languages like Coq, Isabelle, or TLA+, engineers can mathematically prove that the code will behave exactly as intended under all possible execution paths. This removes the reliance on traditional unit testing, which can only prove the presence of bugs, not their absence. Formal verification is increasingly applied to both core consensus node software and the smart contracts that run on top of the blockchain, where a single bug can result in the loss of millions of dollars.
Beyond static data security, the core challenge of any blockchain is reaching agreement on the state of the ledger in a distributed network. Proving the security of consensus mechanisms, such as Proof of Work (PoW) and Proof of Stake (PoS), requires demonstrating two fundamental properties: consistency (or safety) and liveness. Consistency guarantees that all honest nodes agree on the same history of transactions, preventing double-spending. Liveness ensures that new, valid transactions will eventually be processed and added to the ledger, preventing censorship. Proving the security of blockchain protocols
The first layer of proving blockchain security resides in the cryptographic primitives that secure data integrity and identity. Blockchains rely heavily on cryptographic hash functions, such as SHA-256, and digital signature schemes, like ECDSA or Ed25519. To prove the security of these components, cryptographers rely on reductionist security proofs. This method demonstrates that if an adversary can break the cryptographic primitive, they can also solve a known, computationally hard mathematical problem, such as factoring large integers or finding discrete logarithms. For example, the security of a blockchain's Merkle tree depends on the collision resistance of its hash function. By proving that finding a collision is as hard as solving a classically difficult math problem, developers can mathematically guarantee that transaction data cannot be tampered with without detection. While mathematical proofs on paper provide the theoretical
While mathematical proofs on paper provide the theoretical foundation, translating these designs into code introduces the risk of human error and implementation bugs. To bridge this gap, computer scientists utilize formal verification. Formal verification is the act of proving or disproving the correctness of intended algorithms underlying a system with respect to a certain formal specification or property, using mathematical methods. By writing the protocol's specifications and its code in specialized languages like Coq, Isabelle, or TLA+, engineers can mathematically prove that the code will behave exactly as intended under all possible execution paths. This removes the reliance on traditional unit testing, which can only prove the presence of bugs, not their absence. Formal verification is increasingly applied to both core consensus node software and the smart contracts that run on top of the blockchain, where a single bug can result in the loss of millions of dollars.
Beyond static data security, the core challenge of any blockchain is reaching agreement on the state of the ledger in a distributed network. Proving the security of consensus mechanisms, such as Proof of Work (PoW) and Proof of Stake (PoS), requires demonstrating two fundamental properties: consistency (or safety) and liveness. Consistency guarantees that all honest nodes agree on the same history of transactions, preventing double-spending. Liveness ensures that new, valid transactions will eventually be processed and added to the ledger, preventing censorship.
The first layer of proving blockchain security resides in the cryptographic primitives that secure data integrity and identity. Blockchains rely heavily on cryptographic hash functions, such as SHA-256, and digital signature schemes, like ECDSA or Ed25519. To prove the security of these components, cryptographers rely on reductionist security proofs. This method demonstrates that if an adversary can break the cryptographic primitive, they can also solve a known, computationally hard mathematical problem, such as factoring large integers or finding discrete logarithms. For example, the security of a blockchain's Merkle tree depends on the collision resistance of its hash function. By proving that finding a collision is as hard as solving a classically difficult math problem, developers can mathematically guarantee that transaction data cannot be tampered with without detection.