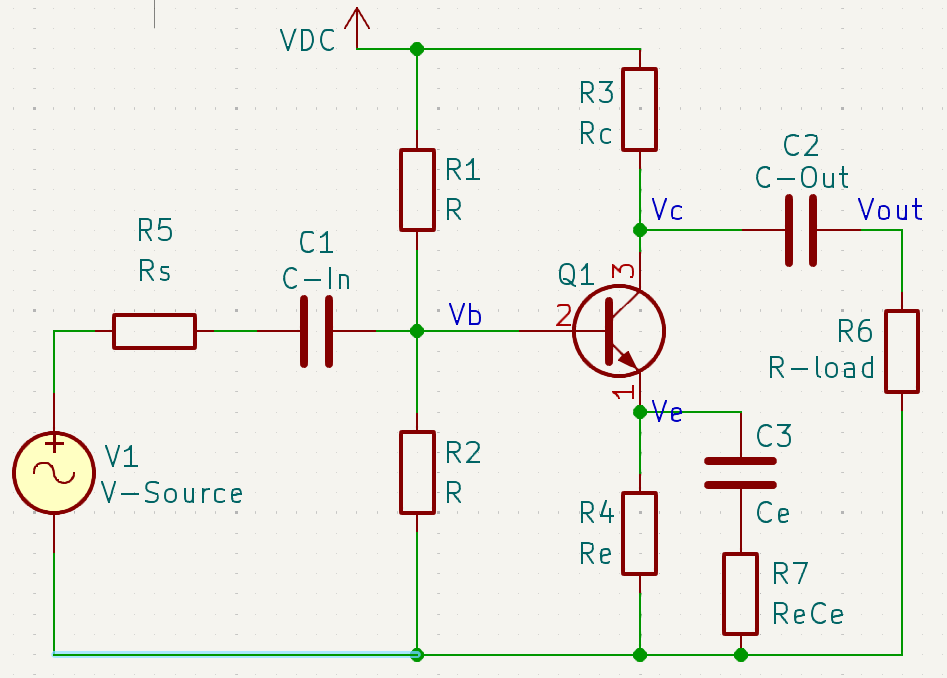
There are different ways to calculate an amplifier, depending on what you want to achieve.
Maybe you want to achieve a certain gain, as far as possible (classic mode). Or you have a low Vcc to respect (modern mode). Or you work with analog audio amps (symmetry mode).
Depending on what you want to achieve and the way of calculating it. Some fields might become dependent on others, or the other way around.
Your above choise makes some input fields available for manipulation, while hiding others.
🎯 1. Target Gain (Av) — "Classic mode" What is a Vulnerability Assessment
You care about how much your amplifier multiplies the input signal.
Set desired voltage gain and Rc voltage drop. Best for learning and simple amplifiers.
You say: “I want a gain of 10.”
The app adjusts resistors to try and match that.
You must give Av and Vrc (the voltage dropped across Rc).
Best for common emitter amplifiers.
✅ Default choice for most beginners and educational use. With cyber threats evolving rapidly—over 40
⚡ 2. Target Emitter Voltage (Ve) — "Modern mode"
You care about setting a healthy DC bias point.
Prioritize stable biasing via Ve. Useful for low-voltage circuits or precision designs.
You say: “I want Ve = 0.5 V, to keep the transistor out of trouble.”
This makes sure your transistor stays in active mode.
Gain becomes whatever it turns out to be.
Ideal for common emitter amplifiers when the goal is to ensure proper biasing for low-voltage or precision circuits, and it’s also used in class AB amplifiers to prevent distortion What is a Vulnerability Assessment
✅ Useful in low-voltage designs (e.g., 3.3V systems).
🧭 3. Target Collector Voltage (Vc) — "Symmetry mode"
You want to place the collector in the middle of the power rail.
Target Vc = Vcc/2 for maximum signal swing. Great for audio and analog signals.
You say: “Make Vc = Vcc/2” for maximum swing.
Useful for analog audio amps or symmetrical headroom.
Gain and Ve are outcomes.
Best for common collector amplifiers and class AB amplifiers.
✅ Best for signal integrity.