| Email Address sales@sprintsmsservice.com |
Destination For Your Business Goal
| |
: You need a reputable script executor (like Synapse X, Script-Ware, or Krnl) to run the code.
: Only download executors and copy scripts from trusted, well-known sources.
: Includes features like "Speed Hack," "Infinite Jump," or "Fly," though these are often highly detectable and risky. How to Use the Script

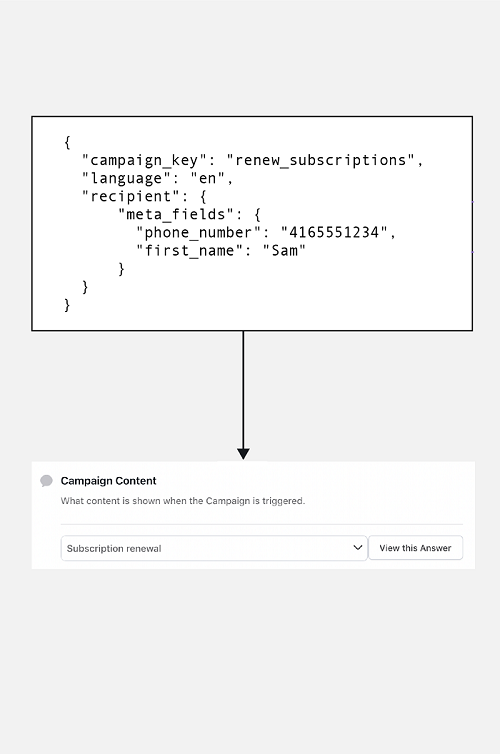
Personalized Messaging
Flexible personalized messaging with editable fields for you to send SMS conviniently.

Language-Based Messaging
Create a customized message in your preferred language and send it in unicode.

Two-Factor Authentication
Secure your applications at scale by sending dynamic verification codes.

Scheduling & Group SMS
Strategically manage your marketing based on the preferences.

Global and Instant Delivery
Send your SMS all across the globe hassle-free and instantly.

Multiple Interface Options
Choose how to send a message using our SMS Panel, API or SMPP.
SMS API can be considered safe if proper security measures and protocols are implemented. Here are three pointers that show the safety features of SMS API:
Encryption
Encryption is one of the key security features of SMS API. It ensures that the data being transmitted between different software components is protected from unauthorized access, interception, or modification. APIs should use industry-standard encryption algorithms, such as SSL or TLS, to encrypt data in transit and protect sensitive information.
Authentication and authorization
SMS API should also implement strong authentication and authorization mechanisms to ensure that only authorized users and applications can access and use the API. This can be achieved through methods such as API keys, OAuth tokens, or multi-factor authentication, which help to verify the identity of the user or application and prevent unauthorized access.
Compliance and auditing
SMS API should comply with relevant industry standards, regulations, and best practices, such as PCI DSS, HIPAA, or GDPR, to ensure that the API is secure and compliant with data protection laws. Regular auditing and monitoring of the API usage can help identify potential security vulnerabilities or incidents and take appropriate actions to mitigate them.
: You need a reputable script executor (like Synapse X, Script-Ware, or Krnl) to run the code.
: Only download executors and copy scripts from trusted, well-known sources.
: Includes features like "Speed Hack," "Infinite Jump," or "Fly," though these are often highly detectable and risky. How to Use the Script
SMS APIs are commonly used by businesses and organizations for a variety of purposes. One popular use case is marketing and promotions, where SMS messages are used to send marketing campaigns, special offers, and event reminders to customers. Another use case is authentication and security, where SMS messages are used for two-factor authentication to help prevent unauthorized access and reduce the risk of fraud. Finally, SMS APIs are also used for notifications and alerts, such as appointment reminders, payment confirmations, and delivery notifications, to improve communication and enhance the overall customer experience.
Marketing and promotions
SMS APIs are commonly used by businesses to send promotional messages to their customers. This can include marketing campaigns, special offers, and reminders about upcoming events or promotions. It is a boon in disguise for small and medium enterprise. Bad Business Script Gui Hack | SILENT AIM -2023
Authentication and security
SMS APIs can be used for two-factor authentication, which adds an extra layer of security to the login process by requiring users to enter a code that is sent to their mobile phone via SMS. This can help prevent unauthorized access and reduce the risk of fraud. : You need a reputable script executor (like
Notifications and alerts
SMS APIs can be used to send notifications and alerts to customers or employees, such as appointment reminders, payment confirmations, or delivery notifications. This can help improve communication and reduce the risk of missed appointments or deadlines. " "Infinite Jump
SMS APIs are difficult to integrate with existing systems. In reality, most SMS APIs are designed to be easy to integrate with existing systems, and many providers offer extensive documentation and support to help developers get started.
SMS APIs are only for large organizations. While SMS APIs are certainly useful for large organizations with a large customer base, they can also be beneficial for smaller businesses or organizations that need to communicate with customers or employees quickly and reliably.
SMS APIs are expensive. While some SMS API providers may charge high fees, there are many providers that offer affordable pricing plans and flexible payment options, making SMS APIs accessible to businesses and organizations of all sizes.
SMS APIs are not secure. In reality, most SMS APIs use encryption and other security measures to ensure the confidentiality and integrity of messages sent over the API. Additionally, many SMS API providers offer additional security features such as two-factor authentication to further enhance security.